What’s Market? A look into Data Breach Notifications
The What’s Market Series
What’s Market is a new series that seeks to delve into the multitude of provisions that exist within a contract and identify their importance, as well as how common they are within vendor, customer and negotiated contracts. All data is gathered by TermScout, which uses attorneys assisted by AI to accurately review and score contracts.
In this article, we look at how common data breach notification provisions are in contracts for IT services, namely software, SaaS, and PaaS contracts. In other words, how often do vendors of IT services contractually promise to notify their customers of a data breach.
What is a Data Breach?
A data breach is typically defined as the loss, theft, or unauthorized access of sensitive or proprietary data. A more robust definition from USLegal can be found here.
Data breaches are serious issues, as the loss of sensitive or proprietary data can cause public embarrassment, significant mitigation expenses, and loss of customer goodwill. In order for affected businesses to mitigate the impacts of a data breach, it is essential for vendors to notify their customers as quickly as possible after a breach event. While most jurisdictions have legislation in place that requires private or government entities to notify individuals of data breaches, these laws do vary from state to state, as do the requirements for notification, making it hard to predict what legal requirements will apply to your situation. For this reason, buyers of IT often prefer to contractually agree to data breach notification policies, which in some cases may be stricter than the legal requirements.
Vendor v. Negotiated Agreements
So, how common are data breach notification provisions in IT contracts? We took a look at 471 standard vendor click through agreements and 60 negotiated contracts to bring you the answer.
There is a split between businesses who must notify a customer of a security breach, and those who are not strictly required to do so. In this section we will explore the differences in the data found between vendor and negotiated contracts.
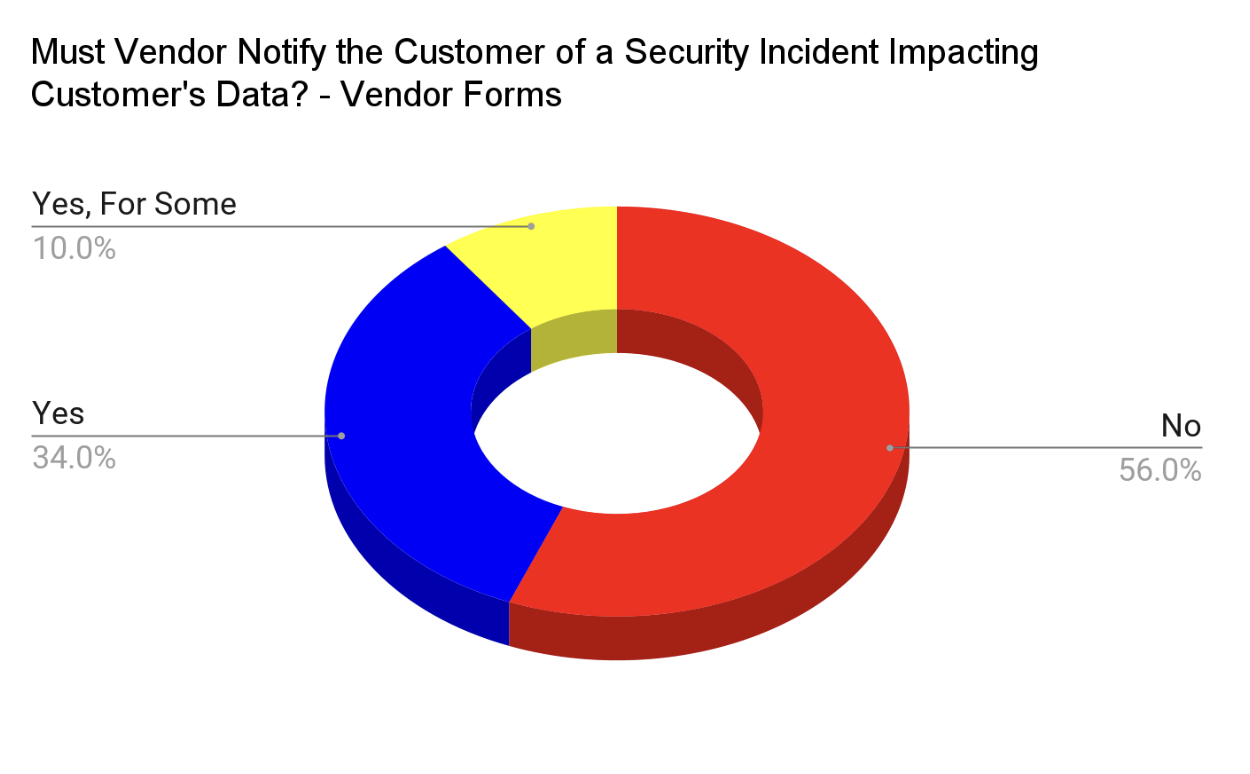
As seen above, most vendor forms either do not contain language that pertains to data breach notification, or state that they are not required to notify the customer when a security incident occurs. Only a small percentage, 34%, contain specific provisions in regard to notification. However, there is a striking contrast when looking at the data for negotiated forms, as seen below.
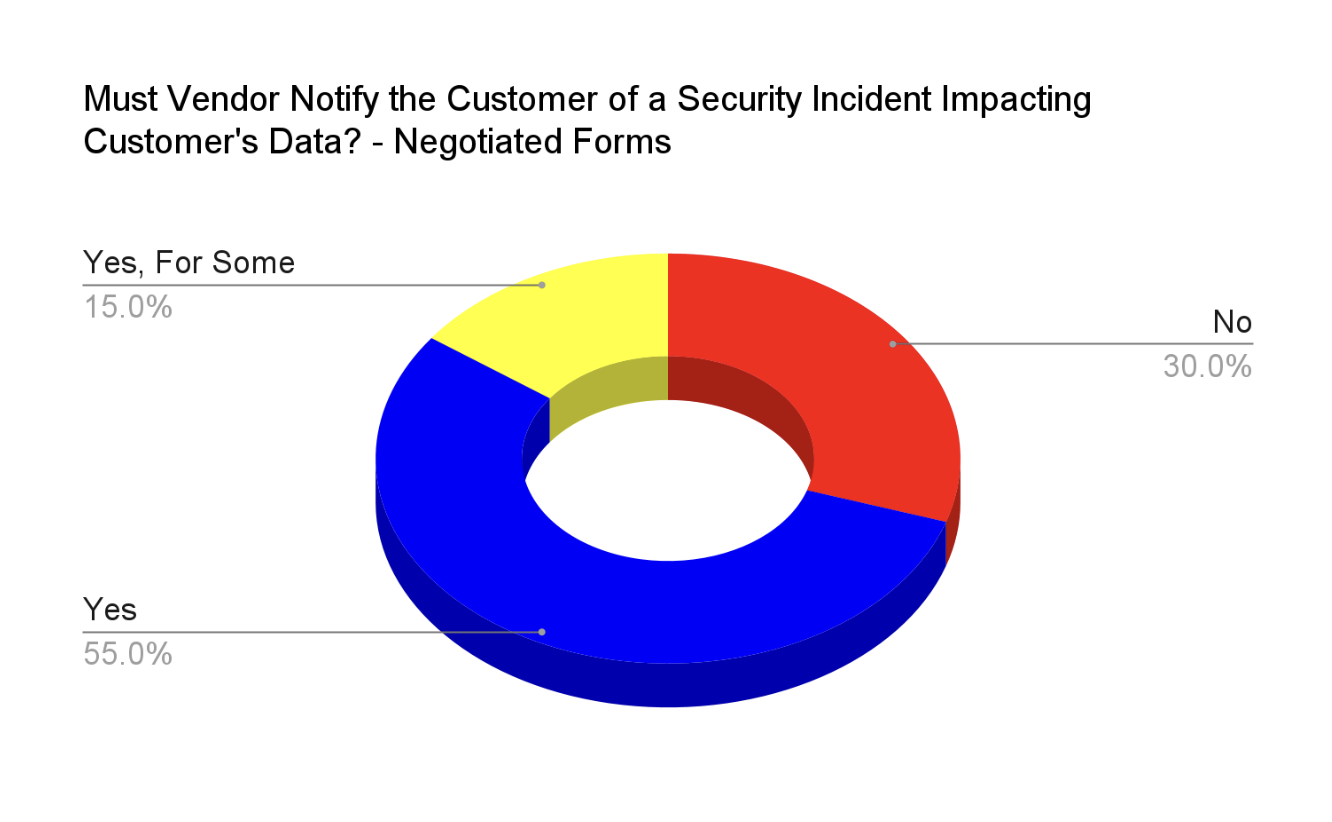
Here we clearly see that over 50% of negotiated forms contain specific language in regard to notifying the customer when a security incident occurs, with an additional 15% requiring notification under limited circumstances. Given the difference in data, it is clear that customers want predictability and assurance as to how and when they will be notified.
Representative Provisions
We’ve included sample provisions for each answer as to whether a business must notify the customer when a security incident impacting the customer’s data occurs. The answers are as follows: No, Yes and Yes, but only under limited circumstances. If you are interested in learning more, you can find all of the data and information presented here and more by visiting TermScout’s Market Insights.
Example #1 – No
[…] In the unlikely event that we believe the security of your Personal Information in our possession or control may have been compromised, we may seek to notify you of that development. If notification is appropriate, we shall endeavor to do so as promptly as possible under the circumstances, and (insofar as we have your e-mail address) we may notify you by e-mail. You consent to our use of e-mail as a means of such notification. If you would prefer us to use another method to notify you in this situation, please e-mail us at info@csod.com with the alternative contact information you would like us to use.
Cornerstone Learning: Security, Privacy Policy
Example #2 – Yes
To the extent Abacus becomes aware and determines that an Incident qualifies as a breach of security leading to misappropriation or accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to, Personal Data transmitted, stored or otherwise Processed on Abacus systems or the applicable cloud environment that compromises the security, confidentiality or integrity of such Personal Data (“Personal Data Breach”), Abacus will inform Client of such Personal Data Breach without undue delay but at the latest within 72 hours.
AbacusNext: 11.3, Data Processing Addendum
Example #3 – Yes, but only under limited circumstances
Sub-processor Accountability Algolia is responsible for the processing of personal information it receives, and subsequently transfers to a third-party acting as an agent on its behalf in accordance with our subscription agreements. Algolia may use from time to time third-party service providers, contractors, and sub-processors to assist in providing the Services on our behalf. Algolia maintains contracts with these third-parties restricting their access, use, and disclosure of personal information
Algolia: 3.2.1, Data Processing Addendum
Final Thoughts
34% of vendors provide unambiguous language about how and when they will notify the customer when a data breach occurs. However, as seen in the data for negotiated forms, this issue is important to customers, with 55% of negotiated contracts containing such a clause. We can draw from this that customers want assurance and predictability when and if a data breach occurs, so that both parties can take the necessary steps to minimize the damage and protect any sensitive information. Before signing a contract, read through it in its entirety and ensure that the provisions relating to data breaches are clear, so that if the worst were to come, you and your business will be prepared.
The What’s Market series will be published regularly, so keep an eye out for the next article on Vendor’s Right to Use Anonymized Data, coming soon.
Share this
You May Also Like
These Related Stories

What’s Market? Protection of Confidential Information
What is the Public Contract Database?

.png?width=130&height=53&name=Vector%20(21).png)